
The harsh reality is that no one is fully protected from cyber threats. If you’re connected to the internet, you’re a target for hackers. As a result, every business must decide its acceptable and unacceptable levels of cybersecurity risk.
If you were to look at your organization’s cybersecurity right now, where do you think your acceptable risk is? What levels of risk do you face or prevent daily? Where would you draw the line in the image below?

Every organization has to decide its own level of “acceptable risk.” The truth is that, in today’s world, it is impossible to have the ideal level of zero risk. If you are connected to the internet, risk exists. But you don’t have to feel helpless.
We wanted to shine light on what each risk levels means and how they are determined. We believe that knowledge is power, and that companies can use this information to determine their level of acceptable risk and how to get there.
WEBIT Services has offered cybersecurity services to clients for over 25 years. In that time, WEBIT has been proactive in learning risks, preventions, and risk responses to help build its clients’ protection against cyber threats. In addition, WEBIT performs quarterly risk assessments to identify and address client cybersecurity risk levels.
By the end of this article, you will learn how risk levels are determined in a risk assessment, the definition of each risk level, and five tools that can lower risks and protect your business.
Simply put, cybersecurity risk is anything that can compromise the security of your network, data, and technology.
The CIS and NIST cybersecurity frameworks recognize various levels of cybersecurity risk. They can be summarized as critical, high, medium, and low levels of risk.
When a risk assessment is conducted, it will use Common Vulnerabilities and Exposures (CVE) to identify risks. The CVE is a glossary of recognized risks, vulnerabilities, and effective reactions determined by cybersecurity framework experts.
The individual risks are then graded using the Common Vulnerability Score System (CVSS or CVE Score).
The CVE score is on a scale from 0-10.
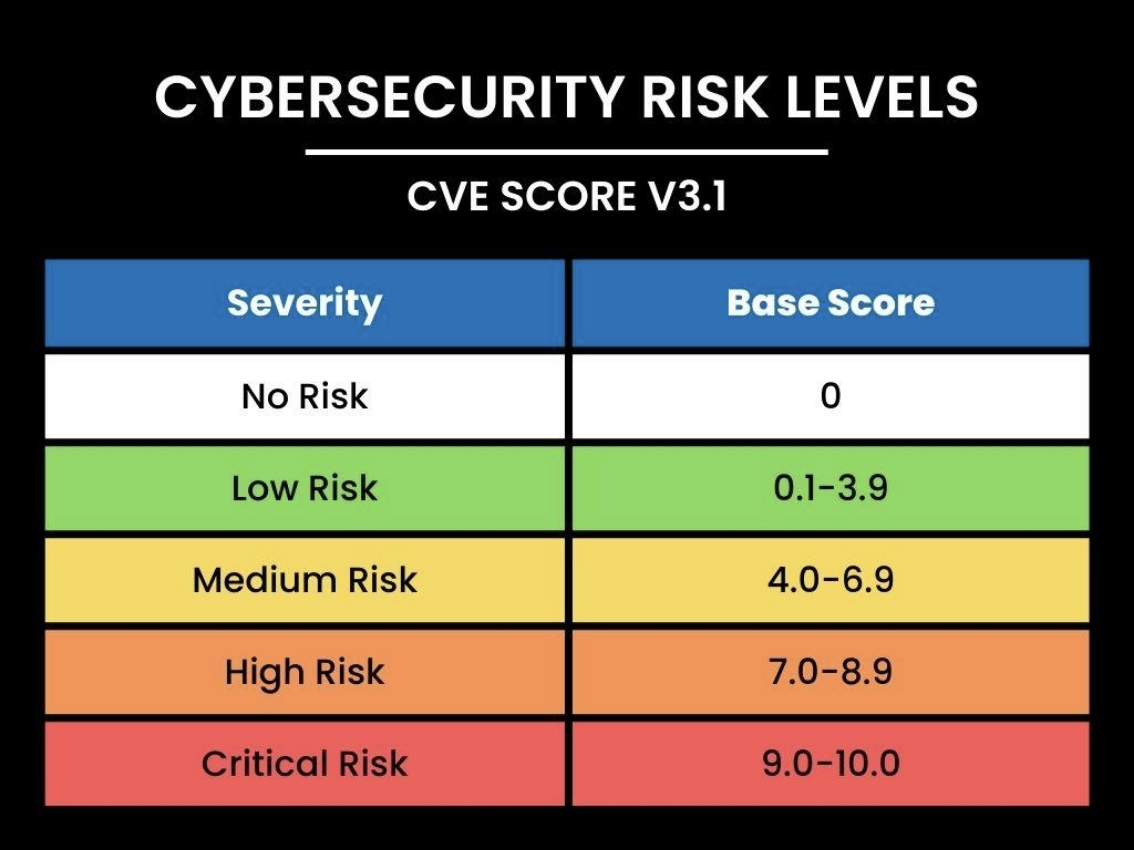
A CVE score is calculated based on the potential damage level and the likelihood of an attack on that vulnerability. Damage levels are rated on a score of 0-6, while likelihood levels are rated from 0-4. The two ratings combined create the final CVE score and risk level.
For example, a new virus is uncovered and is given a moderate damage level of 3.2 out of a possible score of 6.0. However, the likelihood of infection is almost guaranteed, giving it a score of 3.8 out of 4.0. Combining damage and likelihood scores gives the final CVE score of 7.0 out of 10.0. Therefore, the virus is labeled high risk.
Hardware, software, patches, cyber threats, and system activities are all given individual CVE scores in risk assessments.
Each CVE risk level will include possible cyber events of similar damage levels and urgency.
Here are more in-depth definitions and examples of events in risk level.
A critical risk status indicates that a system has a severe and immediate risk of destructive events. These events include cyberattacks or equipment failure that would result in widespread outages, major information breaches, or system shutdowns if not addressed.
These risks also have a high probability of occurring in the very near future.
A critical risk event could include:
A high cybersecurity risk means there is an immediate possibility of harmful events that can compromise systems. High risk is a step down from critical risk but still indicates high impact damaging or disruptive events.
Again, these events are not limited to cyberattacks but include equipment failure.
High risks events also indicate a high probability of exploitation, damage, or disruption if the issues are not addressed quickly.
High-risk events may include:
Medium cybersecurity risk means that there is a chance of malicious activity. The potential damage levels are moderate but not severe.
While not immediately damaging, a medium-risk event can develop into a severe risk if it is not addressed.
Medium risk events may include:
Low cybersecurity risk means there are few anomalies outside the usual concern for cybercrime events.
At a low-risk status, your network activity is deemed normal. No major or dangerous events are occurring in your system. If an issue is detected, it is usually small and easy to address.
However, it’s important to note that zero risk does not exist. If your system is connected to the internet, there is always the risk of a cyberattack.
Low-risk events may include

Hackers use more advanced software and phishing scams to access systems and steal information.
Businesses must ensure that they use the proper programs and practices to help prevent breaches and reduce risk.
Organizations can utilize the following five strategies to help reduce risk.
Your IT provider or internal IT team should base their cybersecurity practices and responses on a framework like NIST or CIS.
These frameworks are created and approved by experts. They are designed and approved by experts. The frameworks are consistently updated to reflect current cyber threats, solutions, and best practices.
If an IT provider is not following a recognized framework, the risk of cyberattacks significantly increases.
Updating hardware and software is integral to building cybersecurity and reducing risk.v
Maintenance patches and software updates are often created in response to identified system weaknesses. Installing recommended updates quickly can help fortify the software or system.
Asset lifecycle management is the practice of monitoring hardware age and functionality. When equipment is too old to regularly update or function well, it is replaced.
Asset lifecycle management asks, “Does the manufacturer still support my technology? Is it protected through updates? How long will this hardware or software be effective? What is its lifespan and where is it on that timeline?”
This practice is part of the IT Roadmap strategy, which helps organizations plan and budget for replacements.
Your organization should be matched with appropriate cybersecurity tools and programs to help decrease cyberattacks.
Your IT provider or internal IT team should match your business to cybersecurity tools that meet your business’s needs. When utilized properly, these programs can identify and detain threats like phishing emails and malware.
Other tools like multi-factor identification can help keep login information safe.
All employees should be trained in good cybersecurity practices. Human intelligence is still a powerful resource in the fight against cybercrime.
Regular, short training sessions and tests should occur to keep employees sharp and aware. Employees who are unaware or unwilling to participate create cybersecurity risks.
At the beginning of the article, we asked you to draw a line to reflect your acceptable risk level.
Now that you’ve learned the definitions for each risk level and how those levels are determined, has that line moved? Do you feel your company’s risk level is higher, lower, or exactly where you want it?

If your current risk levels aren’t where you want them, it may be time to reevaluate your cybersecurity practices or IT Provider.
Now is a perfect time to perform a risk assessment if you’ve never had one or if it’s been more than three months since your last assessment.
When it comes to cybersecurity, knowledge is power. Risk assessments should be performed regularly to identify and address undesirable risks.
WEBIT Services is passionate about helping clients define their acceptable risk levels and reach their cybersecurity goals. We believe education and knowledge are the first steps in building effective cybersecurity practices.
If you’re looking for a new IT provider, schedule a 30-minute consultation to see if WEBIT Services might fit your company.
To learn more about IT incident responses, read our article on Data Backup vs. Continuity article.
If you are in the process of choosing an IT provider, read our Top 9 Questions to ask potential IT providers to identify a quality IT provider.